CBT Nuggets - EC Council CEH Certified Ethical Hacker v8.0 (312-50) (2014)
30xHDRip | MP4/AVC, ~500 kb/s | 1280x720 | Duration: 14:29:45 | English: AAC, 56 kb/s (1 ch) | 3.07 GBGenre: Security, Hacking
This Certified Ethical Hacker v8.0 video training course with James Conrad covers how to legally protect against hacker security breaches, including virtualization, reconnaissance, footprinting, social engineering, scanning, sniffing, cryptography, and more.
Recommended skills:
- Familiarity with Windows of all versions back to Windows XP and Windows Server 2003
- Familiarity with Linux is not necessary but recommended (a video early in the course provides basic Kali Linux training that is sufficient for the learner to complete the course)
Recommended equipment:
Whatever equipment is being used to view the videos (except a smartphone or tablet) is sufficient to create a basic lab environment in which the learner can mirror demonstrations in the videos. This would also require installation of any virtualization software such as Parallels, VMware, Hyper-V, or VirtualBox.
High-speed internet is recommended to download Kali Linux and some of the additional tools.
Related job functions:
- Network Administrator
- Systems Administrator
- Systems Engineer
- Help Desk
Most IT professionals are far too busy with daily tasks and projects to commit themselves to a serious study of security. Problem is, hackers are quite serious about your security and how to exploit it. If a security breach occurs at a company, it can cost millions of dollars, the loss of a priceless reputation, private customer information, and the very jobs of the IT professionals who often get blamed for weak security practices. One of the best ways to ensure good security is to know what hackers do to circumvent it. Security concepts and facts alone do not protect your systems. However, knowledge and experience in exactly how hackers exploit weaknesses will help you to potentially avoid embarrassing security breaches in the future.
1. Course Introduction (4 min)
2. Introduction to Ethical Hacking (20 min)
3. Terms and Types of Hackers (27 min)
4. Virtualization (26 min)
5. Linux (36 min)
6. Reconnaissance: Overview (17 min)
7. Reconnaissance: Powerful Resources (32 min)
8. Footprinting and Countermeasures (28 min)
9. Social Engineering (37 min)
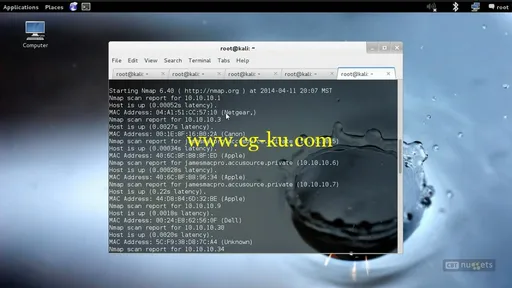
10. Scanning Overview (38 min)
11. Scanning Demos (48 min)
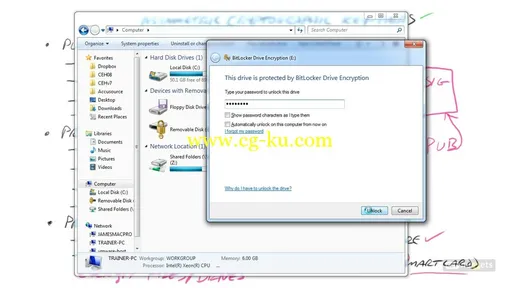
12. Enumeration (47 min)
13. Cracking Windows Passwords (37 min)
14. Password Principles and Cracking Linux Passwords (27 min)
15. System Hacking: ADS and Steganography (23 min)
16. System Hacking: Keyloggers and Metasploit (25 min)
17. Malware (36 min)
18. Hack-O-Rama: Armitage, RAT and Netcat (39 min)
19. Hack-O-Rama: Rootkits and Trojans (25 min)
20. Sniffing Overview (25 min)
21. Sniffing Demos (21 min)
22. Denial of Service (34 min)
23. Hijacking (29 min)
24. Hacking Web Sites and Web Apps: Overview (26 min)
25. Hacking Web Sites and Web Apps: Demos (30 min)
26. Cryptography (39 min)
27. IDS (18 min)
28. Snort and Honeypots (21 min)
29. Wireless Overview (28 min)
30. Wireless Demos (14 min)
31. Mobile Technologies (14 min)