 Implementing Wireless Security in a BYOD Environment
Implementing Wireless Security in a BYOD Environment
949MB | Duration: 5h 03m | Video: AVC (.mp4) 1024x768 15fps | Audio: AAC 48KHz 2ch
Genre: eLearning | Level: Intermediate | Language: English
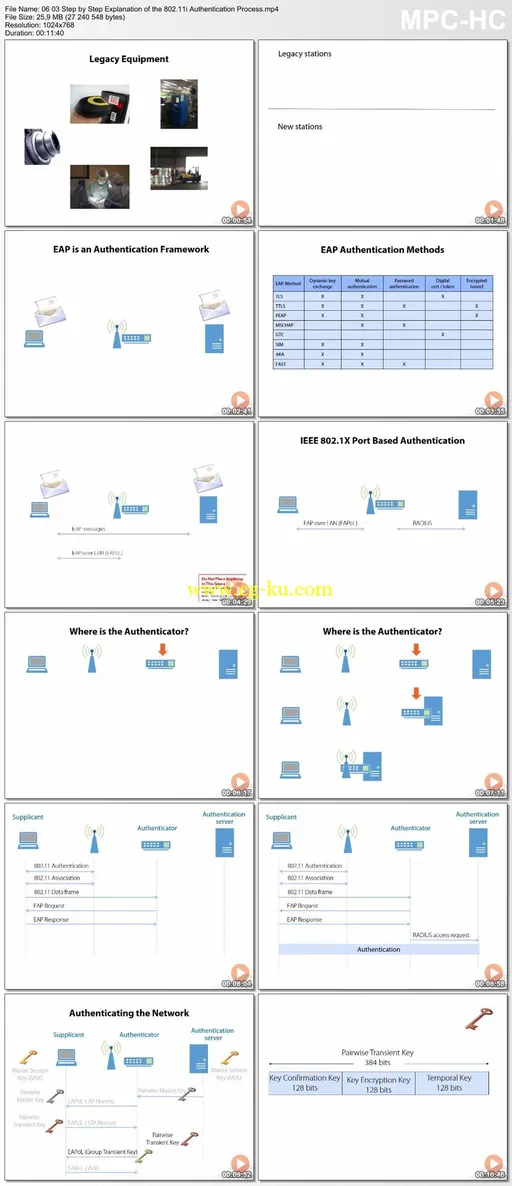
This course explains Wi-Fi security with a focus on implementing WPA2 to meet the growing demands for BYOD. The course begins with a discussion on common wireless attacks, demonstrates how you can detect these attacks, and describes the countermeasures you can put in place to protect your network. Rogue access points, DoS, and use of public hotspots are covered. The course then details the different security mechanisms defined in the 802.11 specifications, starting with the different encryption options, including the risks associated with using WEP and TKIP, and the transition to AES. There is an in-depth look at the different authentication mechanisms, including MAC, 802.1x, and Web-based authentication. The course concludes with a detailed discussion on TKIP and CCMP message authentication, and the new 802.11w mechanism that protects management frames. Details on the security changes made to support the new 802.11ac very high throughput standard are also covered.

发布日期: 2015-02-06