
Secure Coding Rules for Java LiveLessons
English | March 2015 | .FLV | h264, yuv420p, 1280x720, 30.00 fps(r) | aac, 44100 Hz, stereo | 2.98 GB
Genre: E-learning
Java Professional Development LiveLessons provides developers with practical guidance for developing Java programs that are robust and secure. These LiveLessons complement The CERT Oracle Secure Coding Standard for Java
In this video training, Robert provides complementary coverage to the rules in The CERT Oracle Secure Coding Standard for Java, demonstrating common Java programming errors and their consequences using Java 8 and Eclipse. Robert describes language behaviors left to the discretion of JVM and compiler implementers and guides developers in the proper use of Java’s APIs including lang, util, Collections, Concurrency Utilities, Logging, Management, Reflection, Regular Expressions, Zip, I/O, JMX, JNI, Math, Serialization, and JAXP.
Introduction
Lesson 1: Java Security Concepts 1.1 Injection attacks 1.2 Leaking sensitive data 1.3 Denial-of-service attacks
Lesson 2: Input Validation and Data Sanitization (IDS) IDS00-J. Prevent SQL Injection IDS01-J. Normalize strings before validating them IDS03-J. Do not log unsanitized user input IDS04-J. Safely extract files from ZipInputStream IDS06-J. Exclude unsanitized user input from format strings IDS07-J. Do not pass untrusted, unsanitized data to the Runtime.exec() method IDS08-J. Sanitize untrusted data passed to a regex IDS11-J. Perform any string modifications before validation IDS16-J. Prevent XML Injection IDS17-J. Prevent XML External Entity Attacks
Lesson 3: Declarations and Initialization (DCL): DCL00-J. Prevent class initialization cycles
Lesson 4: Expressions (EXP) EXP00-J. Do not ignore values returned by methods EXP01-J. Never dereference null pointers EXP02-J. Do not use the Object.equals() method to compare two arrays EXP03-J. Do not use the equality operators when comparing values of boxed primitives EXP04-J. Do not pass arguments to certain Java Collections Framework methods that are a different type than the collection parameter type EXP06-J. Expressions used in assertions must not produce side effects
Lesson 5: Numeric Types and Operations (NUM) NUM00-J. Detect or prevent integer overflow NUM01-J. Do not perform bitwise and arithmetic operations on the same data NUM02-J. Ensure that division and modulo operations do not result in divide-by-zero errors NUM03-J. Use integer types that can fully represent the possible range of unsigned data NUM04-J. Do not use floating-point numbers if precise computation is required NUM05-J. Do not use denormalized numbers NUM07-J. Do not attempt comparisons with NaN NUM08-J. Check floating-point inputs for exceptional values NUM09-J. Do not use floating-point variables as loop counters NUM10-J. Do not construct BigDecimal objects from floating-point literals NUM11-J. Do not compare or inspect the string representation of floating-point values NUM12-J. Ensure conversions of numeric types to narrower types do not result in lost or misinterpreted data NUM13-J. Avoid loss of precision when converting primitive integers to floating-point
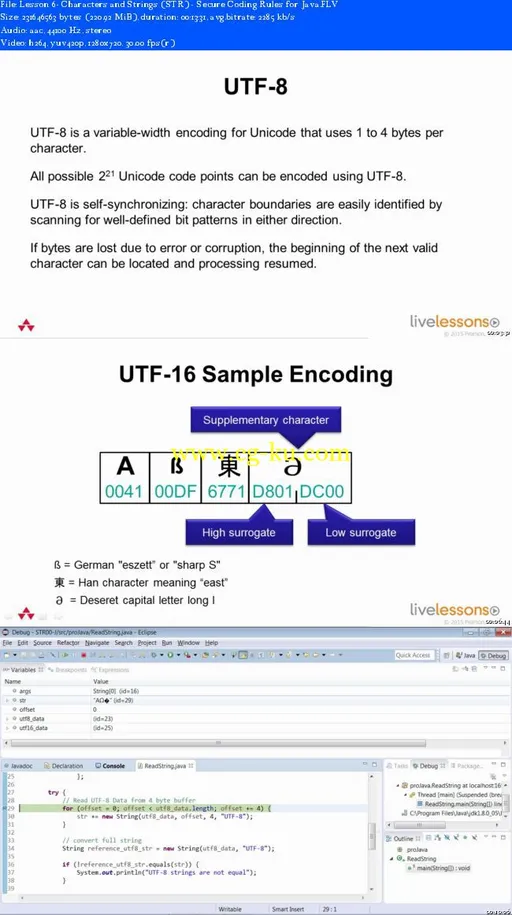
Lesson 6: Characters and Strings (STR) STR00-J. Use an int to capture the return value of methods that read a character or byte STR01-J. Don't form strings containing partial characters STR02-J. Specify an appropriate locale when comparing locale-dependent data STR03-J. Do not convert between strings and bytes without specifying a valid character encoding STR04-J. Use compatible character encodings on both sides of file or network I/O
发布日期: 2015-05-20