MP4 | Video: h264, 1280x720 | Audio: AAC, 44.1 KHz, 2 ChGenre: eLearning | Language: English | + Exercise FilesLevel: Intermediate | Released: 22 Oct 2018Duration: 2h 34m | 388 MBThe prevalence of Cyber Threat Intelligence (CTI) continues to grow within the incident response industry.
This course teaches you how to extract, ingest, pivot on, and hunt for indicators from CTI to help you find what your security tools can't.
Cyber Threat Intelligence (CTI) is all around us.
You can generate intel yourself, pull indicators from a feed, subscribe to a commercial service, or simply extract intel from social media.
However, what do you do with the intel once you obtain it? Many companies simply block atomic indicators within their firewalls and move on with life, but there's so much more to it than that! In this course, Operationalizing Cyber Threat Intel: Pivoting & Hunting, you'll explore how to ingest CTI properly.
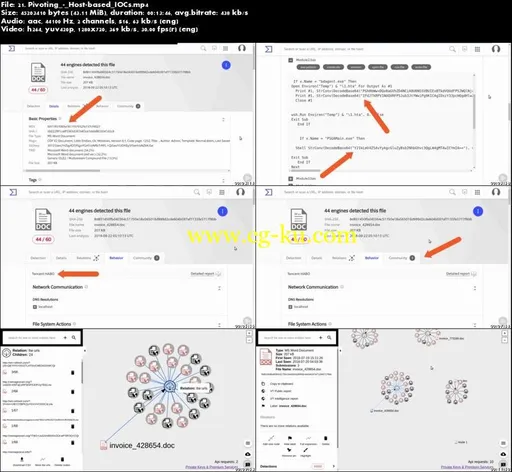
First, you'll learn to make the most of intel articles by extracting all the indicators they provide, even those that aren't obvious.
Next, you'll discover how to pivot on your extracted indicators to provide a more holistic view of the threat.
Finally, you'll touch on some techniques you can use to hunt for indicators within your network.
After taking this course, you'll be better equipped to help protect your organization from threats by reviewing CTI sources and ingesting the information using a skilled, dynamic analysis method.


发布日期: 2018-10-24